9 Ways to Protect Your Social Media Accounts from Hackers
Madison Mohn • 11 July 2022
Why Hackers Want Access to Your Social Media
Your social media accounts share information about who you are, where you go, and what you do daily. When you share pictures on social media, you could be potentially enabling hackers can learn about your online movement. Posts usually include where and when you have taken pictures, meaning hackers can discover where you are and what you do within minutes. They could take confidential data and personal information.
If you want to learn how to protect your social media accounts from hackers and keep you and your loved ones’ accounts safe, consider these nine tips.

1. Create strong passwords
Weak passwords are still too common and pose a dangerous security threat. Many people use easy-to-guess names or numbers to log into secured sites like bank accounts, credit cards, email, and social media platforms.
If you are using simple or duplicate passwords across sites, change them
immediately. Replace them with strong passwords that include special characters and number symbols, mix capital and lowercase letters, and even change your password occasionally. The longer, the stronger.
You can even use a password manager app to help manage passwords, answers to security questions, or other sensitive information for your accounts. Here at Oostas, we use
1Password and find it to have tremendous value. It helps us keep track of the different user IDs and unique passwords so we have improved security without the headache of remembering it all.
2. Set up two-factor authentication
Are you curious about what two-factor authentication is? Two-Factor Authentication (2FA) works by adding an additional layer of security to your online accounts. It requires an additional login credential to gain account access beyond the username, email address, and password.
Two-factor authentication (2FA) applications are a simple and powerful way to protect your accounts from unauthorized access. 2FA apps provide an extra layer of security by requiring users to authenticate their identity with two separate factors: something you know (such as a password) and something you have (such as a smartphone or token).
By using 2FA, even if an attacker obtains your password, they won’t be able to access your account unless they also have physical possession of the device or token used for authentication. These apps use a variety of methods to generate unique one-time passwords (OTPs) which, when coupled with your login credentials, provide an extra layer of security.
Here are links to get you started with setting up 2FA:
3. Avoid suspicious links
Here are some tips to avoid clicking on suspicious links, commonly called phishing. Phishing is a method where cyber criminals send out a mass e-mail containing an attachment or a hyperlink. The attachment is malware, and any hyperlink will be to a website acting as something legitimate that then infects your device.
Do not continue or click links if the sender asks for personal information, has typos, unlikely imagery or layout, and has an odd email address. Check the URL as well. If it’s an
HTTPS address, that additional
S means “secure,” which means there is some level of encryption. Most browsers also include a padlock symbol at the beginning of the address to indicate the site uses encryption.
Social media phishing refers to an attack executed through platforms like Instagram, LinkedIn, Facebook, or Twitter. Such an attack aims to steal personal data or gain control of your social media account. The information gleaned by the hackers includes social media account login credentials, credit card information, and personal information about you, which can then be used to launch other scams and attacks. This could be especially dangerous if it is a business account. They could even continue the scam across your list of followers. It could tarnish your reputation or remove your online presence from potential clients.
4. Stay away from dodgy public Wi-Fi networks
Remember, any device connected to Wi-Fi could be at risk. Free Wi-Fi is available in malls, airports, restaurants, coffee shops, libraries, hotel rooms—you name it. Millions of people use these networks on a daily basis. A hacker could hijack your session and gain access to all of your accounts. Here is some information on safely joining public Wi-Fi.
While cybercriminals can’t read your passwords via Wi-Fi, they could download malware to obtain such data. Another technique is to trick unsuspecting users into joining a fake network put up by the hacker. They will create a close network name like “Coffee Cafe.” That tricks people into joining their network and not the establishment they are in.
5. Steer clear of shady accounts, DMs, or comments
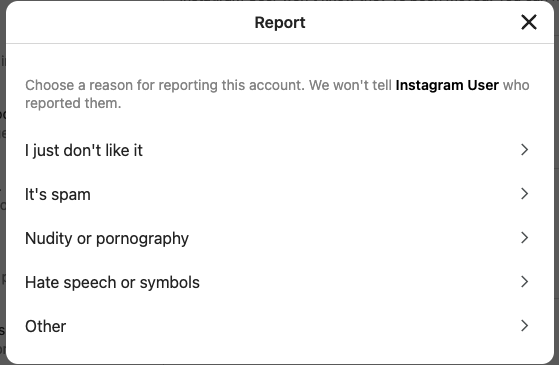
Social media is a magnet for scammers and hackers. If it seems like a fake person or profile wants to follow you, be cautious. Also, be careful of people you do know that start to post questionable content or ask for personal data. Even your closest loved ones’ accounts may be compromised. Once that happens, fraudsters can use those profiles to send out phishing messages—the hacker would love nothing more than for you to be the next victim. Don’t forget to keep yourself and others safe by reporting anything suspicious.
If you get a DM that sounds too good to be true, it most definitely is. In 2022,
Fraud.org warns consumers to be especially wary of scammers seeking them out through these platforms’ direct messaging channels. Instagram direct messaging, Facebook Messenger, or Twitter “DMs” are often where scammers seek to capture a victim’s sensitive information because they allow private, one-on-one conversations. Do not click on the message from these fake accounts, and especially avoid shortened links. They could be designed to steal information. Avoiding these links can prevent hackers from accessing control over your social media accounts.
6. Consider Meta Verified (in beta)
Meta Verified ensures secure and authentic verification for your account. You can verify your identity with a government-issued ID, such as a driver's license or passport, and get access to direct account support. With Meta Verified, you'll also enjoy the benefits of proactive account protection that helps keep your account safe and secure. Get the peace of mind that comes with knowing your personal data is securely verified and protected. Currently available in New Zealand and Australia. However, you can be put on the waiting list to see when it is available in your region.
7.
Monitor Unattended Social Media Accounts
Protecting your accounts from hackers, especially those you no longer use is important. If you have any accounts that are inactive or dormant, it's essential to delete them or at least review the security settings and update passwords as necessary. Make sure there isn't any personal information stored on the account either. Any information stored in an old or unused account is open to exploitation by malicious hackers.
8.
Update Permissions & Privacy Settings
Review app permissions - Many apps request permission to access your account and the data stored within it. Make sure you review them carefully before granting any app access.
Check privacy settings - Social media sites have a range of privacy settings that allow you to control who can see your posts and profile information. Review these settings periodically to ensure they align with what you want to share and protect. By updating your security and privacy settings, you can ensure that your social media accounts remain secure from unwanted access or misuse.
9.
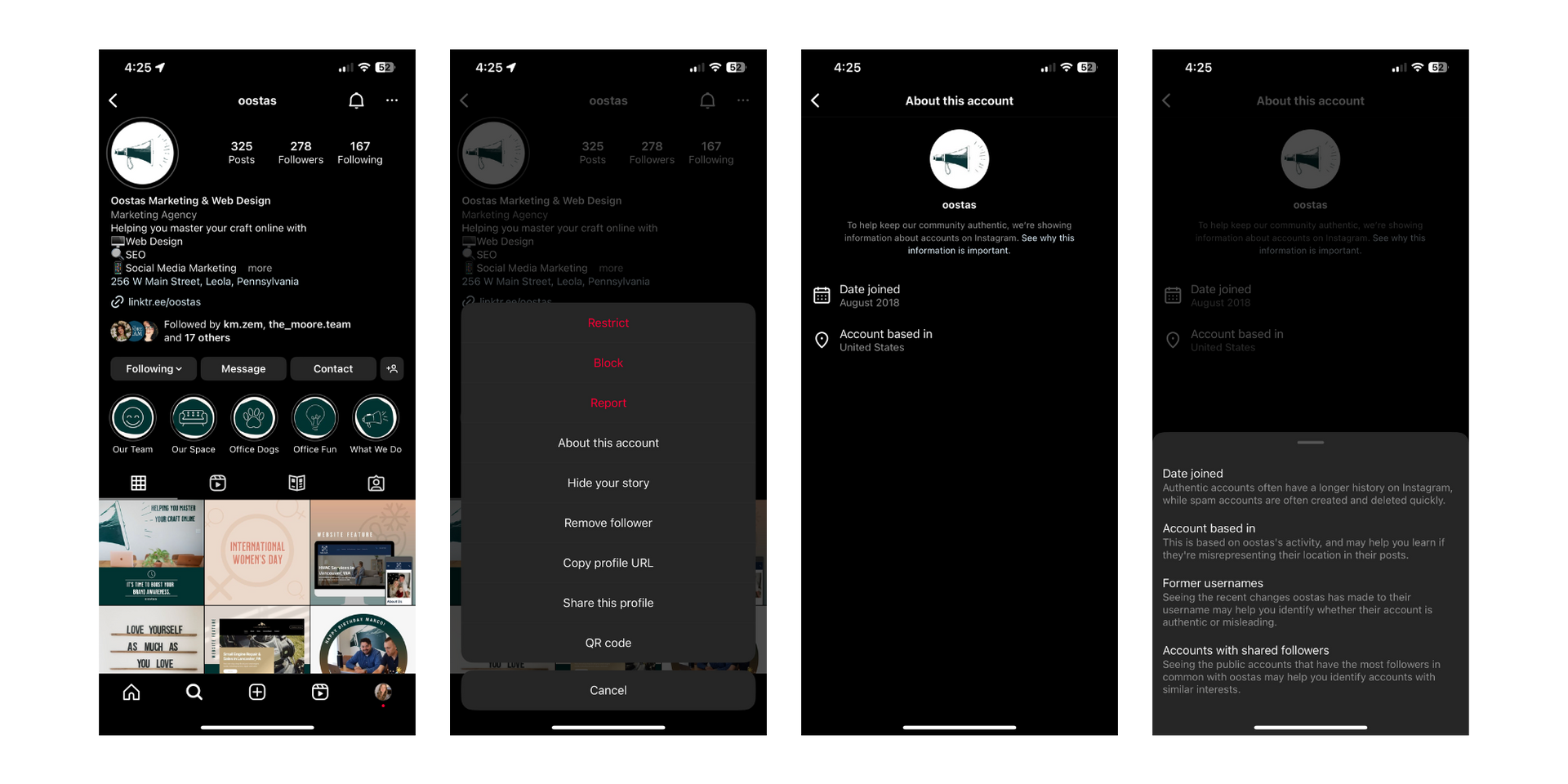
imposter account dangers
Once the fake account is set up, it can be used to post content that looks like it's coming from your business. This can be damaging as customers may not recognize it's a fraudulent account, and they could end up being exposed to malicious links or spam. It’s also hard to undo any damage once it has been done.
To protect your business’s online reputation, it’s essential to be aware of the signs that a fraudulent account has been created. Monitor for any accounts with a username or profile picture similar to your brand, and double-check the information on their profile page. If you find a suspicious account, contact the social media platform to report it. And be sure to remind your customers that any official accounts for your business will only ever come from a verified source. By guarding against fake accounts, you can help ensure your brand’s reputation remains intact and protect your customers from malicious activity.
On Instagram, you can click the three dots on someone's profile to confirm the items below:
These are a few critical measures you can take to secure your social media accounts. By taking these steps ahead of time, it is possible to prevent these attacks from taking place. We must all do our part to protect our online activities and identities from being stolen. Remember to use these tips to help keep your online information safe and secure, and don’t forget to share them with friends and loved ones!
Remember:
- Create strong passwords.
- Always use 2-factor authentication; this way, even if a hacker obtains your username and password, they still won’t be able to access your accounts.
- Avoid suspicious links.
- Turn off automatic Wi-Fi network connection, and make sure you are connected to a trusted network.
- Be wary of suspicious accounts, DMs, or comments, and never click on a link you are unsure of.
- Consider purchasing Meta Verified.
- Delete unattended accounts.
- Check permissions and security settings in your accounts.
- Make sure you don’t fall bait to fake accounts.
By following these tips, you can help ensure that your brand’s social media accounts are safe and secure. It is also important to remember that cybercriminals are constantly adapting their methods, so it’s essential to stay up to date on the latest security measures to ensure your accounts remain secure. At Oostas, we know that social media can prove time-consuming, so if you’d benefit from some
help managing your social, our experts are only a click or call away and can keep your socials safe.